Uninstalling Custom Applications
Using this feature, you can control the installed applications, on which computers, and uninstall any unauthorized applications present on network computers.
To uninstall applications:
1. Select Remediate tab > Remediation Center and click Uninstall Applications.
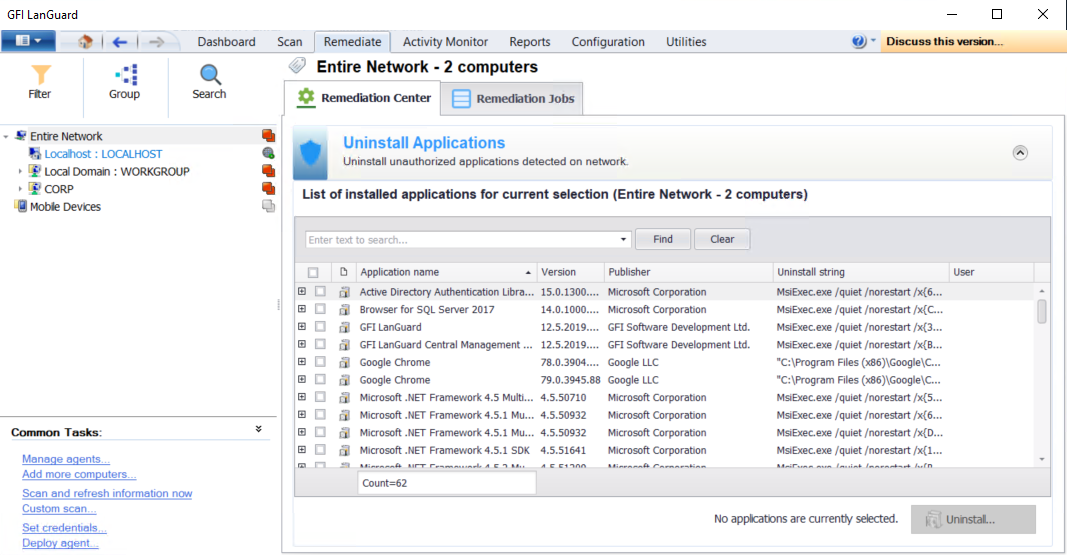
Uninstall applications
2. Expand the application to display the list of computers and select the computers where the application will be uninstalled.
NOTE
The list of applications displayed relies on the unauthorized applications set up for the scanning profile in use. For more information refer to Configuring unauthorized applications auto-uninstall.
3. Repeat step 2 for all applications that will be uninstalled and click Uninstall.
NOTE
Key in a criteria and click Find to search a vulnerability. Click Clear to clear previous search results.
4. Configure the options described below:
| Option | Description |
|---|---|
| Uninstall immediately | Uninstall the selected applications immediately. |
| Uninstall on | Uninstall the selected applications on a specific date and time. Configure when to uninstall the applications. |
| Credentials | Select the authentication method to use or specify a username and password. Select Use per computer credentials when available, to use the credentials specified in the computer properties. For more information refer to Agent properties. |
| Before deployment options | Configure the actions to perform before deploying the selected applications. For more information refer to Configuring auto-remediation options. |
| After deployment options | Configure the actions to perform after deploying the selected applications. For more information refer to Configuring auto-remediation options. |
| Advanced options | Configure other options related to reboot/shut down and delete copied files from remote computers. For more information refer to Configuring auto-remediation options. |
5. Click OK.
6. To view the un–installation progress, click Remediation Jobs from the right panel.