Preparing the server for client access
In a hosting environment you may not have the ability to assist users with the setup of desktop and mobile applications for mailbox access. You can use various technologies and services to simplify the user experience for mailbox setup and access.
Configuring DNS for automatic account configuration
Many messaging applications use Autodiscovery to simplify the configuration of accounts. You can enable this technology in Kerio Connect through proper DNSDomain Name System - Enables the translation of hostnames to IP addresses and provides other domain related information. configuration. Refer to Configuring Autodiscover in Kerio Connect and Configuring DNS for instant messaging for details.
Enabling secure remote access to services
In a hosting environment client applications can access Kerio Connect services from insecure networks. In order to maximize security you can set policies to enforce encrypted and secure methods of remote access.
| Service | Description |
|---|---|
| SSLSecure Sockets Layer - A protocol that ensures integral and secure communication between networks. redirection and enforcement |
Kerio Connect can redirect users to the secure version of the web services and prevent insecure connections. This ensures secure connectivity and prevents the possibility of eavesdropping. For more information refer to Configuring a secure connection to Kerio Connect.. |
| SMTPSimple Mail Transport Protocol - An internet standard used for email transmission across IP networks. Submission |
The Simple Message Transport Protocol (SMTP) protocol is commonly filtered or blocked in residential and public Internet locations. An extension to SMTP called submission uses an alternate port (587) and enables users to authenticate and subsequently relay mail without the same layers of filtering. Make sure this service is available to your server to improve email delivery for your users.. |
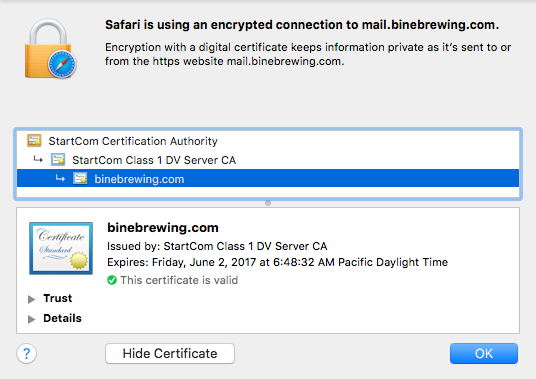
| Certificate Authority (CA) signed certificates |
Kerio Connect includes a self-signed SSL certificateSSL certificates are used to authenticate an identity on a server., however most applications prompt users with disruptive warnings when connecting to secure services that do not have a certificate signed by a trusted authority.
Prompt for a signed certificate For more information refer to Creating certificates signed by a certification authority. |